Member-only story
Intro
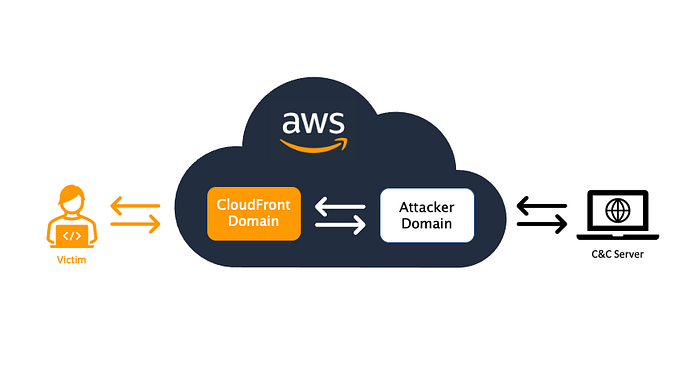
What is Cloud Fronting?
AWS CloudFront is another way to hide your C2 server IP. Once configured, the traffic can be blended in CDN traffic, and it will connect back to the domain that we configure with AWS CloudFront. It also support HTTPS so it can be utilized in the encrypted traffic (unless the target organization has a HTTPS inspection in place).
Infrastructure Setup
1) Cobalt Strike Server Setup (Cloud VM)
First, you need to create a server for your Cobalt Strike server. For this demo, I have created an AWS EC2 that is configured to use external (public) IP.
$ uname -a
Linux ip-xx 5.4.0-1029-aws #30-Ubuntu SMP Tue Oct 20 10:06:38 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux$ curl ipconfig.io
3.21.xx.xx <-- AWS EC2 Public IP
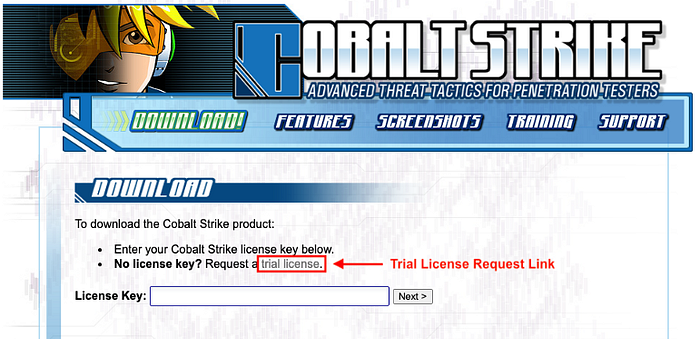
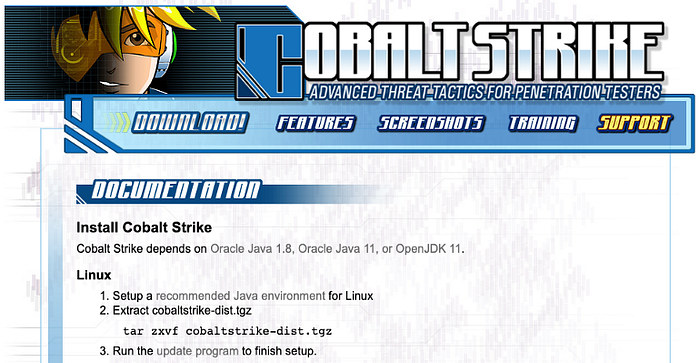
And install Cobalt Strike on that EC2 host using the instruction here.
Note: You will need a valid license or request a free-trial license to download the Cobalt Strike.
2) Attacker’s Domain Setup
Purchasing a Domain
We also need to a domain to use. I will use a new domain that I purchased a while back.
Domain DNS Setup
Configure the DNS “A” record to point to the AWS EC2 host that we created earlier.

- Check the DNS record:
$ nslookup microsoft-securityteam.com
Server: 192.168.1.1
Address: 192.168.1.1#53Non-authoritative answer:
Name: microsoft-securityteam.com
Address: 3.21.28.251
