Member-only story
[RedTeam] Review of Red Team Operations with Cobalt Strike (2019) Training Course (Part 1)

TL;DR
If you ask any red team or adversary simulation operators which tool they use the most, the answer would be Cobalt Strike Command and Control (“C2”). There are actually many other C2 frameworks existing, and some of them have their niche specialties, such as Covenant, .NET C2, and Merlin, HTTP/2 C2. However, in my opinion, what makes Cobalt Strike more attractive than the others is (1) its maturity/stability in use; (2) flexibility of its toolkit; not to mention (3) continuous upgrade/maintenance by the creator, Raphael Mudge who is founder of both SpecterOps and Strategic Cyber LLC and greatly respected offensive security guru.
Speaking of Raphael Mudge, after he announced and released Cobalt Strike 4.0 at the end of 2019, he also published amazing training course of “Red Team Operations with Cobalt Strike (2019).” This course is publicly available at this following YouTube link and consists of 9 video series. The series are around 1-hour or hour-and-half long each. As I wanted to hone my skill sets around red team operations and Cobalt Strike in general, I thought these training series would be perfect for me :)
In this review, I will avoid to talk too much about the actual course contents/materials (because I highly recommend you do go to watch all the video series on your own!); instead, I will try to cover topics he talks about on each series and share some of my notes that I took during the course.
Red Team Ops with Cobalt Strike (1 of 9): Operations
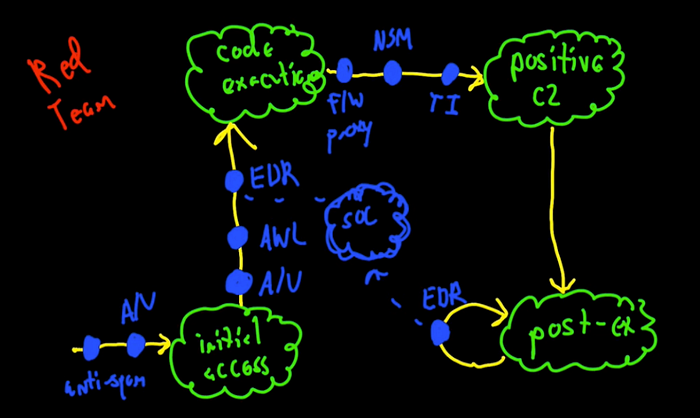
The first one was more introductory video about red team operations, attack kill chain and Cobalt Strike in general. He also talks about what we need to consider when conducting a red team/adversary simulation.
### RedTeam Operational Considerations
│
├──[1] Gaining access via sending phishing emails
│ ├── Anti-malware?
│ ├── Anti-spam?
│ └── Sandbox controls?
│
├──[2] After gaining access to the target host
│ ├── End-point security controls? (e.g., AV)
│ ├──…